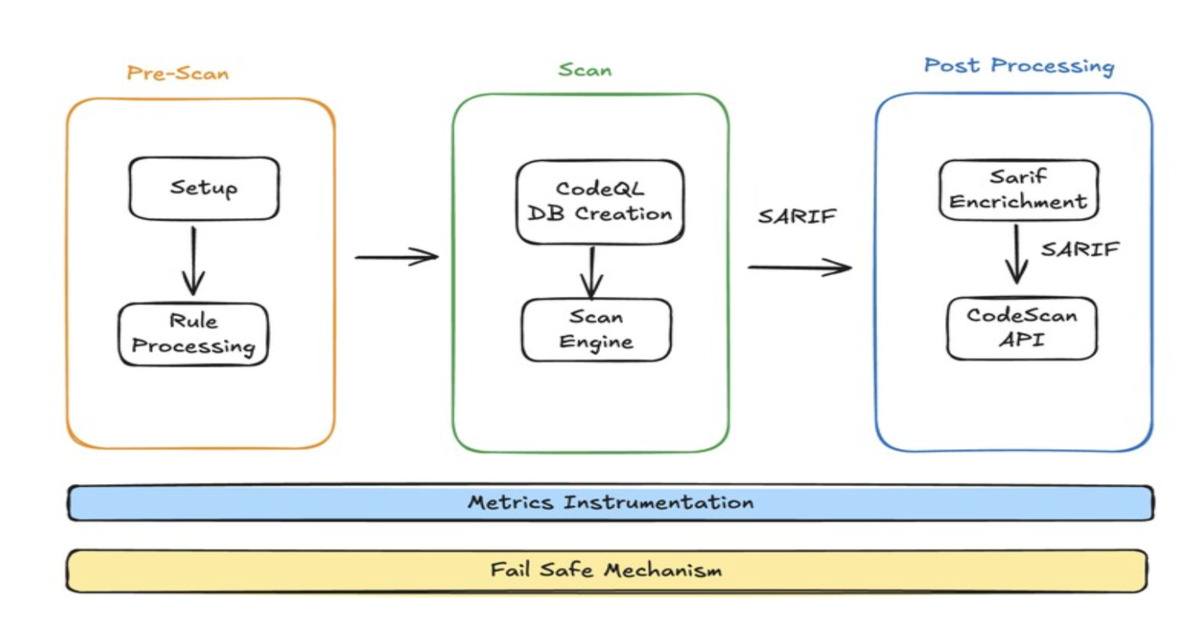
LinkedIn has redesigned its static application security testing pipeline (SAST) to provide consistent, enforceable code scanning across a GitHub-based, multi-repository development environment. The initiative was a result of the company’s shift-left strategy by delivering fast, reliable, and actionable security feedback directly in pull requests, strengthening the security of LinkedIn’s code and infrastructure and helping protect members and customers. At a high level, SAST analyzes source code to identify potential vulnerabilities early in the development lifecycle. At LinkedIn’s scale, legacy approaches that relied on multiple disconnected scanners and custom integrations resulted in uneven coverage, limited visibility into pipeline health, and friction for developers. The redesign aimed to standardize scanning, simplify adoption, and more deeply embed security into developer workflows without introducing bottlenecks. At the start of the redesign, LinkedIn engineers established key guiding principles, prioritizing developer-first security to minimize workflow interruptions, extensibility to allow other teams to add rules or integrations, resilience to prevent failures from affecting developers, and observability to monitor coverage and performance at scale. The new architecture leverages GitHub Actions to orchestrate two primary scanning engines, CodeQL and Semgrep, chosen for their complementary coverage and extensibility. LinkedIn engineers implemented custom workflows to manage rule execution, orchestrate scanning, and
Read More
LinkedIn Leverages GitHub Actions, CodeQL, and Semgrep for Code Scanning – InfoQ
LinkedIn Leverages GitHub Actions, CodeQL, and Semgrep for Code Scanning – InfoQ